Mitigating the risk of identity fraud demands a multifaceted strategy that addresses vulnerabilities on multiple fronts. Establishing robust cybersecurity measures is paramount, encompassing strong passwords, multi-factor authentication, and vigilant monitoring for suspicious activity. Equally important is fostering consciousness among individuals regarding best practices for protecting personal information. This includes being cautious about sharing sensitive data online, verifying the legitimacy of websites before divulging information, and promptly reporting any suspected breaches or fraud attempts.
- Additionally, implementing stringent verification procedures by organizations can significantly curtail the risk of fraudulent activity. This involves conducting thorough background checks, utilizing advanced fraud detection systems, and establishing clear protocols for handling sensitive data.
- Concurrently, a collaborative approach between individuals, businesses, and government agencies is essential to effectively combat identity theft. Sharing information, coordinating responses to breaches, and enacting legislation that strengthens consumer protections are key components of this collective endeavor.
Charting the Labyrinth of copyright Laws: Compliance and Consequences
The world of identification documents can be a treacherous one, particularly when it comes to navigating the complex regulations surrounding copyright. Using a fraudulent ID carries severe consequences, ranging from hefty fines to jail time. Understanding these consequences is paramount for anyone who finds themselves in this circumstance.
Legal experts emphasize the importance of strictly adhering to identification protocols. Authorities utilize sophisticated tools to detect copyright, making it increasingly difficult for individuals to bypass these safeguards. Moreover, the legal repercussions of falsifying identification can have a prolonged impact on one's future opportunities.
- Train yourself about the specific laws and regulations governing identification documents in your jurisdiction.
- Obtain your identification from authorized sources.
- Stay away from participating yourself in any activities that demand the use of copyright.
Remember that the feasible consequences of using a copyright far outweigh any perceived gains. Adherence to legal norms is crucial for guaranteeing a safe and reliable future.
Biometric Security: The Next Frontier in Identity Protection
As technology advances at an unprecedented pace, the need for robust and reliable identity protection has never been greater. Traditional authentication methods, such as passwords and PINs, are increasingly vulnerable to hacking and fraud. Enter biometric security, a revolutionary approach that leverages unique biological traits to verify identities. Biometric systems scan physical or behavioral characteristics, including fingerprints, facial features, iris images, voice signatures, and even gait analysis. These advanced technologies provide a significantly higher level of security compared to conventional methods.
The potential applications of biometric security are vast and growing. From securing sensitive data in corporations to preventing identity theft, biometrics is poised get more info to become the cornerstone of a safer digital world. As research continues to push the boundaries of this technology, we can expect even more powerful biometric solutions in the years to come.
Revolutionizing Identity Verification: Emerging Technologies emerging
The landscape of identity verification is undergoing a radical transformation driven by a surge of sophisticated technologies. These advancements are poised to disrupt the way we authenticate identities, offering greater security and efficiency. From fingerprint recognition to cryptography, these tools are paving the way the future of identity management.
One of the most impactful trends in this space is the adoption of deep learning algorithms. These sophisticated systems can analyze vast amounts of data to identify patterns and anomalies that may indicate fraud.
Furthermore, blockchain technology is gaining traction as a secure and transparent way to store identity information. Its distributed nature makes it extremely difficult to tamper with, providing stronger protection against cyberattacks.
Ultimately, the convergence of these emerging technologies is accelerating a new era of identity verification. Therefore, individuals and organizations alike can expect greater security, usability, and assurance in the digital realm.
Credentials Beyond Passwords: Secure Access with Advanced Biometrics
The traditional reliance on passwords for securing access is increasingly vulnerable to breaches. Cybercriminals are constantly developing new methods to exploit these credentials, leaving individuals and organizations vulnerable. Fortunately, advanced biometrics offer a more reliable alternative for authentication. By leveraging unique biological traits, such as fingerprints, facial scan, or iris scans, biometric systems provide a significantly higher level of defense. These methods are imitate, making them an ideal solution for protecting sensitive data and systems.
- Additionally, biometrics can simplify the user experience by eliminating the need to remember complex passwords.
- As a result, they reduce the risk of unauthorized access.
Tackling Identity Theft: A Collective Effort in Prevention and Response
Identity theft remains a escalating threat in our increasingly electronic world. It's essential to recognize that combating this menace requires a collaborative effort from both individuals and institutions. Individual vigilance is paramount, as adopting strong security practices can significantly reduce the risk of becoming a victim. This includes employing unique passwords for each account, being cautious about sharing personal information online, and regularly reviewing bank statements and credit reports for any suspicious activity. Furthermore, organizations have a duty to establish robust security measures to protect sensitive data. This comprises things like security protocols, employee training on best practices, and timely response to possible breaches. By working jointly, we can create a protected environment for everyone.
 Alicia Silverstone Then & Now!
Alicia Silverstone Then & Now!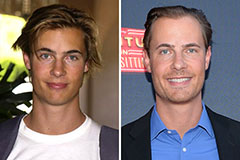 Erik von Detten Then & Now!
Erik von Detten Then & Now! Christy Canyon Then & Now!
Christy Canyon Then & Now! Nicki Minaj Then & Now!
Nicki Minaj Then & Now! Kerri Strug Then & Now!
Kerri Strug Then & Now!